Mobile application security are indispensable tool for large enterprises, enhancing productivity, streamlining operations, and fostering customer engagement. As we know, with the proliferation of mobile apps comes an increased risk of security vulnerabilities. Understanding and mitigating these risks is crucial for protecting sensitive data, maintaining customer trust, and ensuring regulatory compliance. This article delves into common security vulnerabilities in mobile applications and introduces advanced security technologies to help large businesses safeguard their digital assets.
Common Security Vulnerabilities
1. Insecure Data Storage
Many mobile applications store sensitive data on devices without adequate encryption, making it susceptible to unauthorized access. This can lead to data breaches, identity theft, and financial losses.
How to avoid:
- – use strong encryption algorithms for data storage;
- – implement secure key management practices;
- – regularly update and patch applications to address known vulnerabilities.
2. Weak Server-Side Controls
Server-side vulnerabilities occur when applications fail to adequately validate and sanitize inputs from client devices. This can result in SQL injection, cross-site scripting (XSS), and other attacks that compromise backend systems.
How to avoid:
- – employ robust input validation and sanitization techniques;
- – conduct regular security audits and penetration testing;
- – use web application firewalls (WAFs) to detect and block malicious traffic.
3. Inadequate Authentication and Authorization
Weak authentication mechanisms, such as easily guessable passwords or lack of multi-factor authentication (MFA), can allow unauthorized access to application functions and data.
How to avoid :
- – implement MFA to add an extra layer of security;
- – enforce strong password policies;
- – use biometric authentication where possible.
4. Poor Code Quality
Unsecure coding practices can introduce vulnerabilities that attackers can exploit. Common issues include buffer overflows, insecure API usage, and hardcoded credentials.
How to avoid:
- – adopt secure coding standards and best practices;
- – use automated code analysis tools to identify vulnerabilities;
- – conduct regular code reviews and security testing.
5. Insufficient Transport Layer Protection
Data transmitted between mobile applications and servers must be adequately protected to prevent interception and tampering. Insufficient transport layer protection can expose sensitive data to man-in-the-middle (MitM) attacks.
How to avoid:
- – use Transport Layer Security (TLS) to encrypt data in transit;
- – regularly update and configure TLS protocols to ensure they remain secure;
- – validate server certificates to prevent MitM attacks.

Introducing Advanced Security Technologies
1. Application Shielding
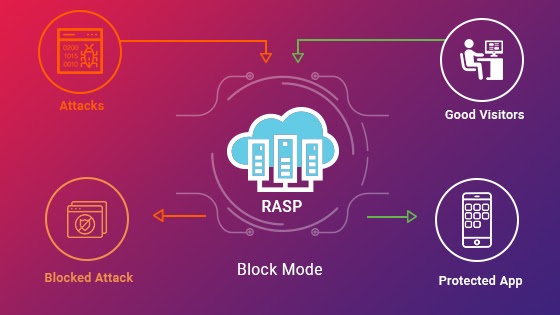
Application shielding techniques, such as code obfuscation and runtime application self-protection (RASP), help protect mobile apps from reverse engineering and tampering.
Benefits:
- – obfuscation makes it difficult for attackers to understand and modify the application code;
- – RASP detects and blocks attacks in real-time, providing continuous protection.
2. Behavioral Analytics
Behavioral analytics use machine learning to analyze user behavior and detect anomalies that may indicate malicious activity. This proactive approach helps identify threats before they can cause significant harm.
Benefits:
- – enhanced detection of sophisticated attacks that bypass traditional security measures;
- – continuous learning and adaptation to evolving threats.

3. Zero Trust Architecture
A Zero Trust approach assumes that threats can originate from both outside and inside the network. This model enforces strict access controls and continuously verifies the identity and trustworthiness of users and devices.
Benefits:
- – minimized risk of insider threats and lateral movement by attackers;
- – granular access controls ensure that only authorized users can access sensitive data.

4. Mobile Threat Defense (MTD)
MTD solutions provide comprehensive protection against mobile-specific threats, including malware, phishing, and network attacks. These solutions integrate with enterprise mobility management (EMM) systems to enhance overall security posture.
Benefits:
- – real-time threat detection and response;
- – improved visibility into mobile device security.

Conclusion
Mobile application security is a critical concern for large enterprises, given the increasing reliance on mobile apps for business operations. By understanding common security vulnerabilities and adopting advanced security technologies, businesses can significantly enhance their security posture. Investing in security consulting services can provide expert guidance and support in implementing robust security measures, ensuring that mobile applications remain secure against evolving threats.